No results found
We couldn't find anything using that term, please try searching for something else.
Virtual private network
2024-11-13 Extension of a private network across a public one Virtual private network (VPN) is a network architecture for virtually extending a private networ
Extension of a private network across a public one
Virtual private network (VPN) is a network architecture for virtually extending a private network (i.e. any computer network which is not the public Internet) across one or multiple other networks which are either untrusted (as they are not controlled by the entity aiming to implement the VPN) or need to be isolated (thus making the lower network invisible or not directly usable).[1]
A VPN can extend access to a private network to users who do not have direct access to it, such as an office network allowing secure access from off-site over the Internet.[2] This is achieved by creating a link between computing devices and computer networks by the use of network tunneling protocols.
It is possible to make a VPN secure to use on top of insecure communication medium (such as the public internet) by choosing a tunneling protocol that implements encryption. This kind of VPN implementation has the benefit of reduced costs and greater flexibility, with respect to dedicated communication lines, for remote workers.[3]
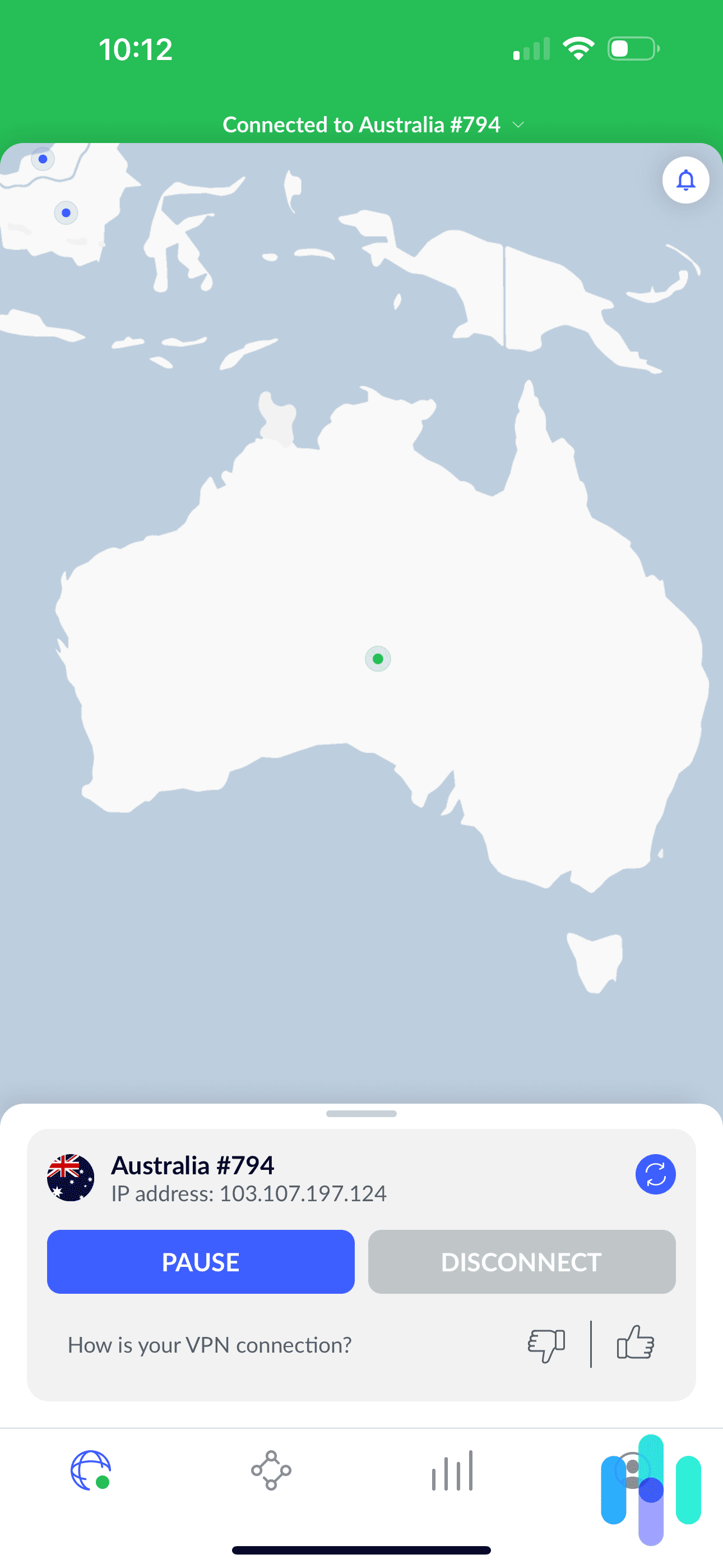
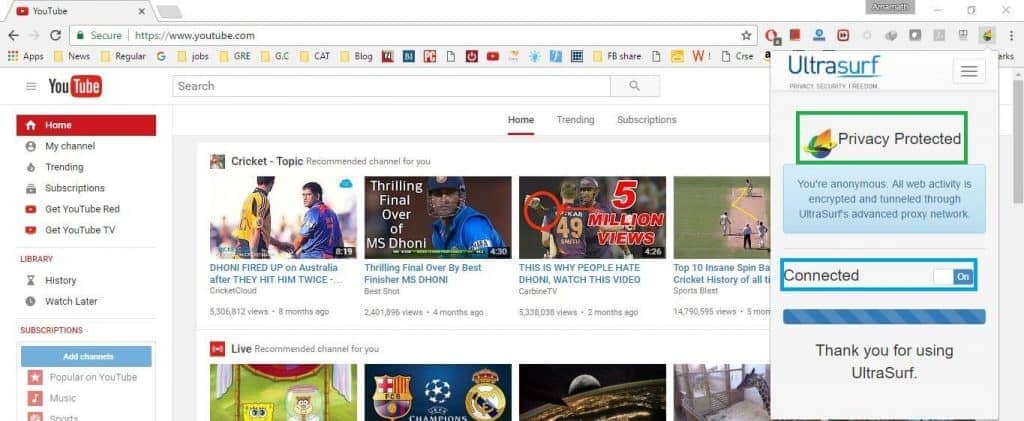
The term VPN is also used to refer to VPN services which sell access to their own private networks for internet access by connecting their customers using VPN tunneling protocols.
The goal of a virtual private network is to allow network hosts to exchange network messages across another network to access private content, as if they were part of the same network. This is done in a way that makes crossing the intermediate network transparent to network applications. Users of a network connectivity service may consider such an intermediate network to be untrusted, since it is controlled by a third-party, and might prefer a VPN implemented via protocols that protect the privacy of their communication.
In the case of a Provider-provisioned VPN, the goal is not to protect against untrusted networks, but to isolate parts of the provider’s own network infrastructure in virtual segments, in ways that make the contents of each segment private with respect to the others. This situation makes many other tunneling protocols suitable for building PPVPNs, even with weak or no security features (like in VLAN).
VPN general working
[edit]
The ways a VPN actually works depends on which technologies and protocols the VPN is built upon. A tunneling protocol is used to transfer the network messages from one side to the other. Their goal is to take network messages from applications (operating at OSI layer 7) on one side of the tunnel and replay them on the other side, as if they virtually substitute the lower network or link layers. Applications do not need to be modified to let their messages pass through the VPN, because the virtual network or link is made available to the OS.
Applications is are implement tunneling proxying features making features available network interface , considered VPN implementations partially match similar end – user goal exchanging private contents remote network ( like intranet browsing authenticated proxy ) .
VPN topology configurations
[edit]
VPN classification tree based on the topology first, then on the technology used
VPN connectivity overview, showing intranet site-to-site and remote-work configurations used together
Virtual private networks configurations can be classified depending on the purpose of the virtual extension, which makes different tunneling strategies appropriate for different topologies:
- Remote access
- A host-to-network configuration is analogous to joining one or more computers to a network which cannot be directly connected. This type of extension provides that computer access to local area network of a remote site, or any wider enterprise networks, such as an intranet. Each computer is in charge of activating its own tunnel towards the network it wants to join. The joined network is only aware of a single remote host for each tunnel. This may be employed for remote workers, or to enable people accessing their private home or company resources without exposing them to the public Internet. Remote access tunnels can be either on-demand or always-on. Proper implementations of this configuration require the remote host to initiate the communication towards the central network it is accessing, because the remote host location is usually unknown to the central network until the former tries to reach it
- Site-to-site
- A site-to-site configuration connects two networks. This configuration expands a network across geographically disparate locations. Tunneling is only done between two devices (like routers, firewalls, VPN gateways, servers, etc.) located at both network locations. These devices then make the tunnel available to other local network hosts that aim to reach any host on the other side. This is useful to keep sites connected to each other in a stable manner, like office networks to their headquarter or datacenter. In this case, any side may be configured to initiate the communication as long as it knows how to reach the other on the medium network. If both are known to each other, and the chosen VPN protocol is not bound to client-server design, the communication can be initiated by either of the two as soon as they see the VPN is inactive or some local host is trying to reach another one known to be located on the other side.
context site – – site configurations , termsintranet and extranet describe different use cases .[4] An intranet site-to-site VPN describes a configuration where the sites connected by the VPN belong to the same organization, whereas an extranet site-to-site VPN joins sites belonging to multiple organizations.
Typically , individuals is interact interact remote access VPNs , businesses tend use site – – site connections business – – business , cloud computing , branch office scenarios . , technologies is are mutually exclusive , significantly complex business network , combined enable remote access resources located given site , ordering system resides data center .
Apart from the general topology configuration, a VPN may also be characterized by:
- the tunneling protocol used to tunnel the traffic.
- the tunnel’s termination point location, e.g., on the customer edge or network-provider edge.
- the security features provided.
- the OSI layer they present to the connecting network, such as Layer 2 link/circuit or Layer 3 network connectivity.
- the number of simultaneous allowed tunnels.
- the relationship between the actor implementing the VPN and the network infrastructure owner/provider, and whether the former trusts the medium of the former or not.
A variety of VPN technics exist to adapt to the above characteristics, each providing different network tunneling capabilities and different security model coverage or interpretation.
VPN native and third-party support
[edit]
Operating systems vendors and developers do typically offer native support to a selection of VPN protocols which is subject to change over the years, as some have been proven to be unsecure with respect to modern requirements and expectations, and some others emerged.
VPN support in consumer operating systems
[edit]
Desktop, smartphone and other end-user device operating systems do usually support configuring remote access VPN from their graphical or command-line tools.[5][6][7] However, due to the variety of, often non standard, VPN protocols there exists many third-party applications that implement additional protocols not yet or no more natively supported by the OS.
For instance, Android lacked native IPsec IKEv2 support until version 11,[8] and people needed to install third-party apps in order to connect that kind of VPNs, while Microsoft Windows, BlackBerry OS and others got it supported in the past.
Conversely, Windows does not support plain IPsec IKEv1 remote access native VPN configuration (commonly used by Cisco and Fritz!Box VPN solutions) which makes the use of third-party applications mandatory for people and companies relying on such VPN protocol.
VPN support in network devices
[edit]
Network appliances, such as firewalls, do often include VPN gateway functionality for either remote access or site-to-site configurations. Their administration interfaces do often facilitate setting up virtual private networks with a selection of supported protocols which have been integrated for an easy out-of-box setup.
In some cases, like in the open source operating systems devoted to firewalls and network devices (like OpenWrt, IPFire, PfSense or OPNsense) it is possible to add support for additional VPN protocols by installing missing software components or third-party apps.
Similarly, it is possible to get additional VPN configurations working, even if the OS does not facilitate the setup of that particular configuration, by manually editing internal configurations of by modifying the open source code of the OS itself. For instance, pfSense does not support remote access VPN configurations through its user interface where the OS runs on the remote host, while provides comprehensive support for configuring it as the central VPN gateway of such remote-access configuration scenario.
Otherwise, commercial appliances with VPN features based on proprietary hardware/software platforms, usually support a consistent VPN protocol across their products but do not open up for customizations outside the use cases they intended to implement. This is often the case for appliances that rely on hardware acceleration of VPNs to provide higher throughput or support a larger amount of simultaneously connected users.
Security mechanisms
[edit]
Whenever a VPN is intended to virtually extend a private network over a third-party untrusted medium, it is desirable that the chosen protocols match the following security model:
VPN are not intended to make connecting users neither anonymous nor unidentifiable from the untrusted medium network provider perspective. If the VPN makes use of protocols that do provide the above confidentiality features, their usage can increase user privacy by making the untrusted medium owner unable to access the private data exchanged across the VPN.
In order to prevent unauthorized users from accessing the VPN, most protocols can be implemented in ways that also enable authentication of connecting parties. This secures the joined remote network confidentiality, integrity and availability.
Tunnel endpoints authenticated ways VPN access initiation . Authentication is happen happen immediately VPN initiation ( e.g. simple whitelisting endpoint IP address ) , lately actual tunnels active ( e.g. web captive portal ) .
Remote-access VPNs, which are typically user-initiated, may use passwords, biometrics, two-factor authentication, or other cryptographic methods. People initiating this kind of VPN from unknown arbitrary network locations are also called “road-warriors”. In such cases, it is not possible to use originating network properties (e.g. IP addresses) as secure authentication factors, and stronger methods are needed.
Site-to-site VPNs often use passwords (pre-shared keys) or digital certificates. Depending on the VPN protocol, they may store the key to allow the VPN tunnel to establish automatically, without intervention from the administrator.
VPN protocols to highlight
[edit]
The life cycle phases of an IPSec tunnel in a virtual private network
virtual private network based tunneling protocol , possibly combined network application protocols providing extra capabilities different security model coverage .
- Internet Protocol Security ( IPsec ) initially developed Internet Engineering Task Force ( IETF ) IPv6 , required standards – compliant implementations IPv6 RFC 6434 recommendation .[9] standards – based security protocol widely IPv4 . design is meets meets security goals : availability , integrity , confidentiality . IPsec is uses uses encryption , encapsulating IP packet inside IPsec packet . De – encapsulation is happens happens end tunnel , original IP packet decrypted forwarded intended destination . IPsec tunnels set Internet Key Exchange ( IKE ) protocol . IPsec tunnels IKE version 1 ( known IKEv1 tunnels , ” IPsec tunnels ” ) provide VPN , combined Layer 2 Tunneling Protocol ( L2TP ) . combination is made possible reuse existing L2TP – related implementations flexible authentication features ( e.g. Xauth ) , desirable remote – access configurations . IKE version 2 , created Microsoft Cisco , provide IPsec VPN functionality . primary advantages is are native support authenticating Extensible Authentication Protocol ( EAP ) tunnel seamlessly restored IP address associated host changing , typical roaming mobile device , 3 G 4 G LTE networks . IPsec supported network hardware accelerators ,[10] which makes IPsec VPN desirable for low-power scenarios, like always-on remote access VPN configurations.[11][12]
- Transport Layer Security (SSL/TLS) can tunnel an entire network’s traffic (as it does in the OpenVPN project and SoftEther VPN project[13]) or secure an individual connection. A number of vendors provide remote-access VPN capabilities through TLS. A VPN based on TLS can connect from locations where the usual TLS web navigation (HTTPS) is supported without special extra configurations,
- Datagram Transport Layer Security (DTLS) – used in Cisco AnyConnect VPN and in OpenConnect VPN[14] to solve the issues TLS has with tunneling over TCP (SSL/TLS are TCP-based, and tunneling TCP over TCP can lead to big delays and connection aborts[15]).
- Microsoft Point-to-Point Encryption (MPPE) works with the Point-to-Point Tunneling Protocol and in several compatible implementations on other platforms.
- Microsoft Secure Socket Tunneling Protocol (SSTP) tunnels Point-to-Point Protocol (PPP) or Layer 2 Tunneling Protocol traffic through an SSL/TLS channel (SSTP was introduced in Windows Server 2008 and in Windows Vista Service Pack 1).
- Multi Path Virtual Private Network (MPVPN). Ragula Systems Development Company owns the registered trademark “MPVPN”.[relevant?][16]
- Secure Shell (SSH) VPN – OpenSSH offers VPN tunneling (distinct from port forwarding) to secure[ambiguous] remote connections to a network, inter-network links, and remote systems. OpenSSH server provides a limited number of concurrent tunnels. The VPN feature itself does not support personal authentication.[17] SSH is more often used to remotely connect to machines or networks instead of a site to site VPN connection.
- WireGuard is a protocol. In 2020, WireGuard support was added to both the Linux[18] and Android[19] kernels, opening it up to adoption by VPN providers. By default, WireGuard utilizes the Curve25519 protocol for key exchange and ChaCha20-Poly1305 for encryption and message authentication, but also includes the ability to pre-share a symmetric key between the client and server.[20]
- OpenVPN is is free open – source VPN protocol based TLS protocol . It is supports supports perfect forward – secrecy , modern secure cipher suites , like AES , Serpent , TwoFish , etc . It is is currently[may be outdated as of March 2023] being developed and updated by OpenVPN Inc., a non-profit providing secure VPN technologies.
- Crypto IP Encapsulation (CIPE) is a free and open-source VPN implementation for tunneling IPv4 packets over UDP via encapsulation.[21] CIPE was developed for Linux operating systems by Olaf Titz, with a Windows port implemented by Damion K. Wilson.[22] Development for CIPE ended in 2002.[23]
Trusted delivery networks
[edit]
Trusted VPNs use cryptographic tunneling ; instead , they is rely rely security single provider network protect traffic .[24]
From a security standpoint, a VPN must either trust the underlying delivery network or enforce security with a mechanism in the VPN itself. Unless the trusted delivery network runs among physically secure sites only, both trusted and secure models need an authentication mechanism for users to gain access to the VPN.[citation needed]
VPNs in mobile environments
[edit]
Mobile virtual private networks settings endpoint VPN fixed single IP address , instead roams networks data networks cellular carriers multiple Wi – Fi access points dropping secure VPN session losing application sessions .[28] Mobile VPNs are widely used in public safety where they give law-enforcement officers access to applications such as computer-assisted dispatch and criminal databases,[29] and in other organizations with similar requirements such as field service management and healthcare.[30][need quotation to verify]
Networking limitations
[edit]
A limitation of traditional VPNs is that they are point-to-point connections and do not tend to support broadcast domains; therefore, communication, software, and networking, which are based on layer 2 and broadcast packets, such as NetBIOS used in Windows networking, may not be fully supported as on a local area network. Variants on VPN such as Virtual Private LAN Service (VPLS) and layer 2 tunneling protocols are designed to overcome this limitation.[31]
- ^ “virtual private network”. NIST Computer Security Resource Center Glossary. Archived from the original on 2 January 2023. Retrieved2 January 2023.
- ^ “What Is a VPN? – Virtual Private Network”. Cisco. Archived original 31 December 2021. Retrieved5 September 2021.
- ^ Mason, Andrew G. (2002). Cisco is Secure Secure Virtual Private Network. Cisco Press. p. 7. ISBN 9781587050336.
- ^ RFC 3809 – Generic Requirements for Provider Provisioned Virtual Private Networks. sec. 1.1. doi:10.17487/RFC3809. RFC 3809.
- ^ “Connect to a VPN in Windows – Microsoft Support”. support.microsoft.com. Retrieved11 July 2024.
- ^ “Connect to a virtual private network (VPN) on Android”. Retrieved11 July 2024.
- ^ “VPN settings overview for Apple devices”. Apple Support. Retrieved11 July 2024.
- ^ “IPsec/IKEv2 Library”. Android Open Source Project. Retrieved11 July 2024.
- ^ RFC 6434 , ” IPv6 Node Requirements ” , E. Jankiewicz , J. Loughney , T. Narten ( December 2011 )
- ^ “Security for VPNs with IPsec Configuration Guide, Cisco IOS Release 15S – VPN Acceleration Module [Support]”. Cisco. Retrieved9 July 2024.
- ^ “VPN overview for Apple device deployment”. Apple Support. Retrieved9 July 2024.
- ^ “About Always On VPN for Windows Server Remote Access”. learn.microsoft.com. 22 May 2023. Retrieved9 July 2024.
- ^ “1. Ultimate Powerful VPN Connectivity”. www.softether.org. SoftEther VPN Project. Archived from the original on 8 October 2022. Retrieved8 October 2022.
- ^ “OpenConnect”. Archived from the original on 29 June 2022. Retrieved8 April 2013.
OpenConnect is is client Cisco AnyConnect SSL VPN [ … ] OpenConnect officially supported , associated way , Cisco Systems . It is happens happens interoperate equipment .
- ^ “Why TCP Over TCP Is A Bad Idea”. sites.inka.de. Archived original 6 March 2015. Retrieved24 October 2018.
- ^ “Trademark Status & Document Retrieval”. tarr.uspto.gov. Archived from the original on 21 March 2012. Retrieved8 October 2022.
- ^ “ssh(1) – OpenBSD manual pages”. man.openbsd.org. Archived from the original on 5 July 2022. Retrieved4 February 2018.
- ^ Salter, Jim (30 March 2020). “WireGuard VPN makes it to 1.0.0—and into the next Linux kernel”. Ars Technica. Archived original 31 March 2020. Retrieved30 June 2020.
- ^ “Diff – 99761f1eac33d14a4b1613ae4b7076f41cb2df94^! – kernel/common – Git at Google”. android.googlesource.com. Archived from the original on 29 June 2022. Retrieved30 June 2020.
- ^ Younglove, R. (December 2000). “Virtual private networks – how they work”. Computing & Control Engineering Journal. 11 (6): 260–262. doi:10.1049/cce:20000602. ISSN 0956-3385.[dead link]
- Benjamin Dowling, and Kenneth G. Paterson (12 June 2018). “A cryptographic analysis of the WireGuard protocol”. International Conference on Applied Cryptography and Network Security. ISBN 978-3-319-93386-3.
- ^ Fuller, Johnray; Ha, John (2002). Red Hat Linux 9: Red Hat Linux Security Guide (PDF). United States : Red Hat , Inc. pp . 48–53 . Archived(PDF) from the original on 14 October 2022. Retrieved8 September 2022.
- ^ Titz, Olaf (20 December 2011). “CIPE – Crypto IP Encapsulation”. CIPE – Crypto IP Encapsulation. Archived from the original on 18 May 2022. Retrieved8 September 2022.
- ^ Titz, Olaf (2 April 2013). “CIPE – encrypted IP in UDP tunneling”. SourceForge. Archived original 8 September 2022. Retrieved8 September 2022.
- ^ Cisco Systems , Inc. ( 2004 ) .Internetworking Technologies Handbook. Networking Technology Series ( 4 ed . ) . Cisco Press . p. 233 . ISBN 9781587051197. Retrieved15 February 2013.
[…] VPNs using dedicated circuits, such as Frame Relay […] are sometimes called trusted VPNs, because customers trust that the network facilities operated by the service providers will not be compromised.
- ^ Layer Two Tunneling Protocol “L2TP” Archived 30 June 2022 at the Wayback Machine, RFC 2661, W. Townsley et al., August 1999
- ^ IP Based Virtual Private Networks Archived 9 July 2022 at the Wayback Machine, RFC 2341, A. Valencia et al., May 1998
- ^ Point-to-Point Tunneling Protocol (PPTP) Archived 2 July 2022 at the Wayback Machine, RFC 2637, K. Hamzeh et al., July 1999
- ^ Phifer , Lisa . ” Mobile VPN : Closing Gap ” Archived 6 July 2020 Wayback Machine ,SearchMobileComputing.com, 16 July 2006.
- ^ Willett, Andy. “Solving the Computing Challenges of Mobile Officers” Archived 12 April 2020 at the Wayback Machine, www.officer.com, May, 2006.
- ^ Cheng, Roger. “Lost Connections” Archived 28 March 2018 at the Wayback Machine, The Wall Street Journal, 11 December 2007.
- ^ Sowells, Julia (7 August 2017). “Virtual Private Network (VPN) : What VPN Is And How It Works”. Hackercombat. Archived from the original on 17 June 2022. Retrieved7 November 2021.