No results found
We couldn't find anything using that term, please try searching for something else.
Tutorial
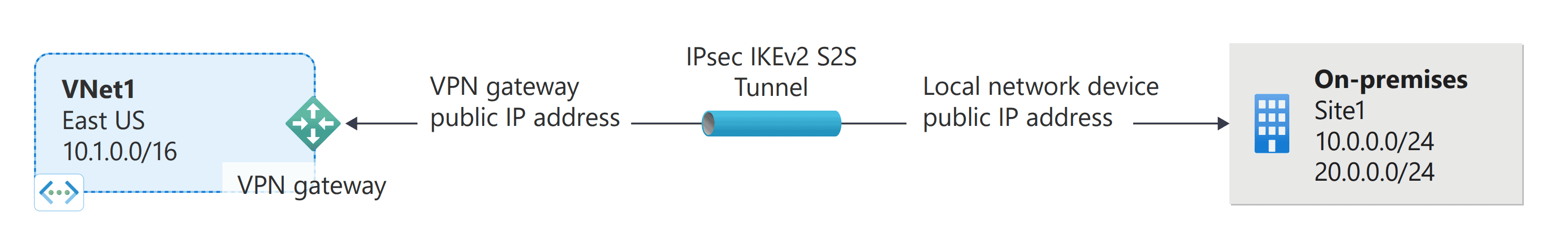
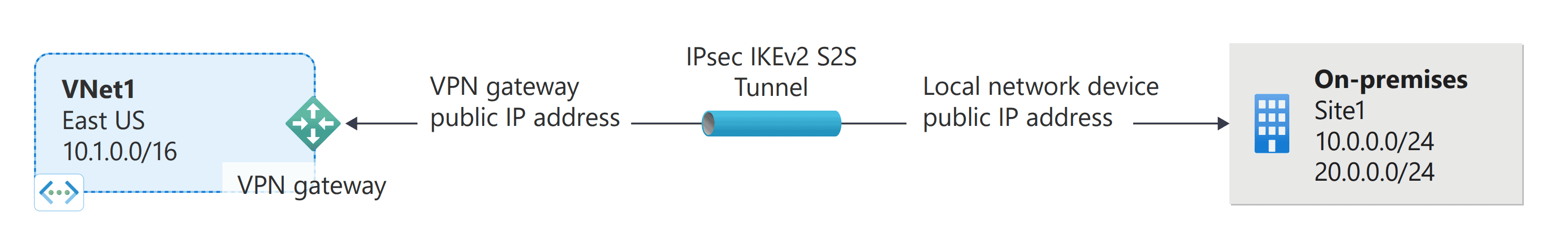
2024-11-13 Tutorial: Create a site-to-site VPN connection in the Azure portal Article08/13/2024 In this article In this tutorial, you use the
Tutorial: Create a site-to-site VPN connection in the Azure portal
- Article
In this tutorial, you use the Azure portal to create a site-to-site (S2S) VPN gateway connection between your on-premises network a virtual network. You can also create this configuration by using Azure PowerShell the Azure CLI.
In this tutorial, you:
- Create a virtual network.
- Create a VPN gateway.
- Create local network gateway .
- Create a VPN connection.
- Verify the connection.
- Connect virtual machine .
Prerequisites
-
You need an Azure account with an active subscription. If you don’t have one, you can create one for free.
-
If you’re unfamiliar with the IP address ranges located in your on-premises network configuration, you need to coordinate with someone who can provide those details for you. When you create this configuration, you must specify the IP address range prefixes that Azure routes to your on-premises location. None of the subnets of your on-premises network can overlap with the virtual network subnets that you want to connect to.
-
VPN devices :
- Make sure you have a compatible VPN device someone who can configure it. For more information about compatible VPN devices device configuration, see About VPN devices.
- Verify that you have an externally facing public IPv4 address for your VPN device.
- Verify that your VPN device supports active-active mode gateways. This article creates an active-active mode VPN gateway, which is recommended for highly available connectivity. Active-active mode specifies that both gateway VM instances are active uses two public IP addresses, one for each gateway VM instance. You configure your VPN device to connect to the IP address for each gateway VM instance. If your VPN device doesn’t support this mode, don’t enable this mode for your gateway. For more information, see Design highly available connectivity for cross-premises VNet-to-VNet connections About active-active mode VPN gateways.
Create a virtual network
In this section, you create a virtual network by using the following values:
- Resource group: TestRG1
- Name: VNet1
- Region: ( ) East
- IPv4 address space: 10.1.0.0/16
- Subnet: FrontEnd
- Subnet address space:
Note
When you use a virtual network as part of a cross-premises architecture, be sure to coordinate with your on-premises network administrator to carve out an IP address range that you can use specifically for this virtual network. If a duplicate address range exists on both sides of the VPN connection, traffic will route in an unexpected way. Additionally, if you want to connect this virtual network to another virtual network, the address space can’t overlap with the other virtual network. Plan your network configuration accordingly.
-
Sign in to the Azure portal.
-
In Search resources, service, docs (G+/) at the top of the portal page, enter virtual network. SelectVirtual network from the Marketplace search results openVirtual network page .
-
On theVirtual network page, select Create openCreate virtual network page .
-
On theBasics tab, configure the virtual network settings for Project details Instance details. You see a green check mark when the values you enter are validated. You can adjust the values shown in the example according to the settings that you require.
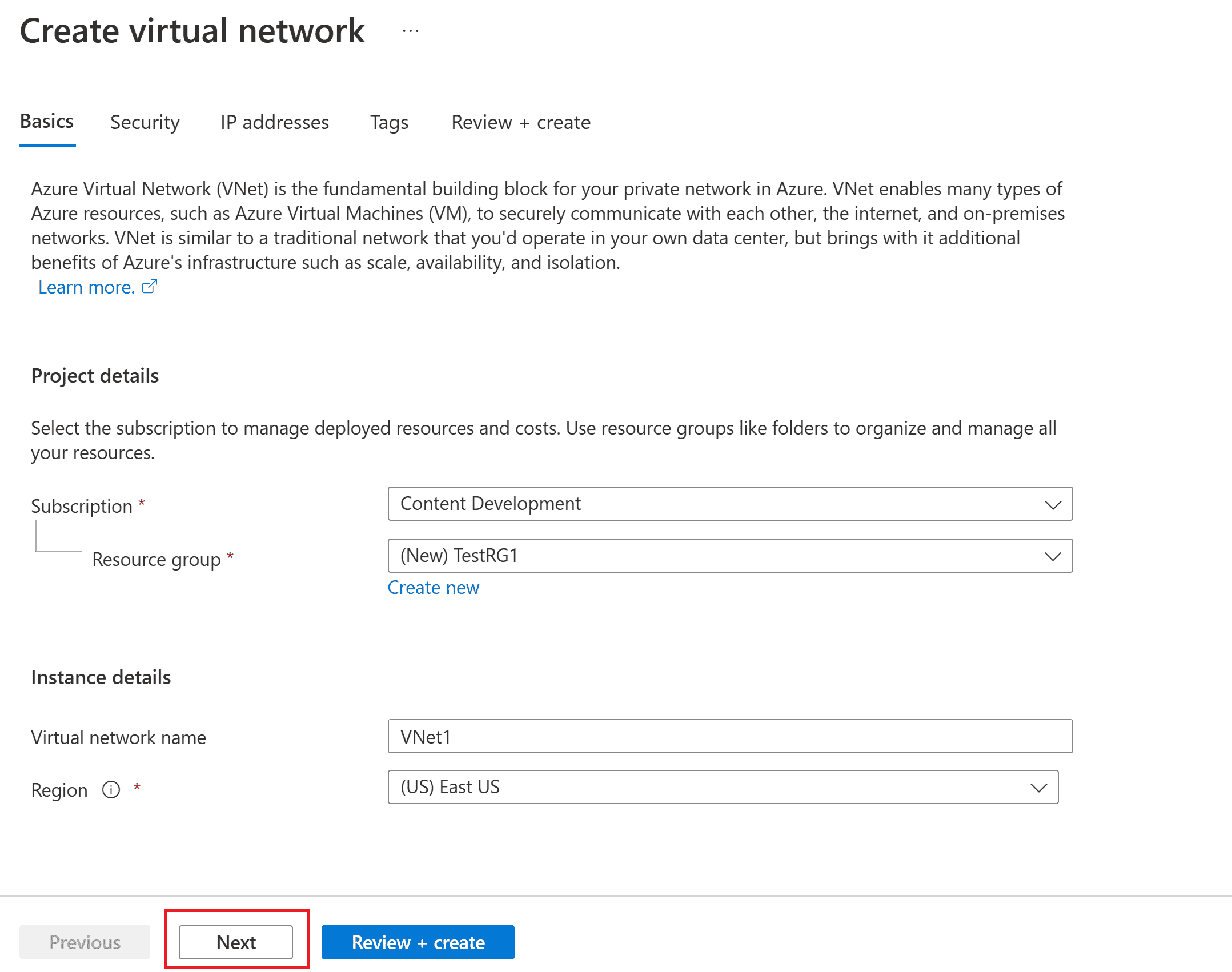
- Subscription: Verify subscription listed correct . You is change change subscriptions dropdown box .
- Resource group: Selectan existing resource group select Create new to create a new one. For more information about resource groups, see Azure Resource Manager overview.
- Name: Enter the name for your virtual network.
- Region: Selectthe location for your virtual network. The location determines where the resources that you deploy to this virtual network will reside.
-
SelectNext Security to go to the Security tab. For this exercise, leave the default values for all the services on this page .
-
SelectIP Addresses to go to the IP Addresses tab. On theIP Addresses tab, configure the settings.
-
IPv4 address space: By default, an address space is automatically created. You can select the address space adjust it to reflect your own values. You can also add a different address space remove the default that was automatically created. For example, you can specify the starting address as 10.1.0.0 specify the address space size as /16. Then select Add add address space .
-
+ Add subnet: If you use the default address space, a default subnet is created automatically. If you change the address space, add a new subnet within that address space. Select+ Add subnet openAdd subnet window. Configure the following settings, then select Add at the bottom of the page to add the values.
- Subnet: You can use the default, specify the name. Example: FrontEnd.
- Subnet address range: The address range for this subnet. Examples are 10.1.0.0 /24.
-
-
Review the IP addresses page remove any address spaces subnets that you don’t need.
-
SelectReview + create to validate the virtual network settings.
-
After the settings are validated, select Create to create the virtual network.
After you create your virtual network, you can optionally configure Azure DDoS Protection. Azure DDoS Protection is simple to enable on any new existing virtual network, it requires no application resource changes. For more information about Azure DDoS Protection, see What is Azure DDoS Protection?.
Create a gateway subnet
The virtual network gateway requires a specific subnet named GatewaySubnet. The gateway subnet is part of the IP address range for your virtual network contains the IP addresses that the virtual network gateway resources services use.
When you create the gateway subnet, you specify the number of IP addresses that the subnet contains. The number of IP addresses needed depends on the VPN gateway configuration that you want to create. Some configurations require more IP addresses than others. It’s best to specify /27 larger (/26, /25, etc.) for your gateway subnet.
- On thepage for your virtual network, on the left pane, select Subnets openSubnets page .
- At the top of the page, select + Gateway subnet openAdd subnet pane.
- The name is automatically entered as GatewaySubnet. Adjust IP address range value , necessary . example is is10.1.255.0/27.
- Don’t adjust the other values on the page . SelectSave at the bottom of the page to save the subnet.
Important
Network security groups (NSGs) on the gateway subnet are not supported. Associating a network security group to this subnet might cause your virtual network gateway (VPN ExpressRoute gateways) to stop functioning as expected. For more information about network security groups, see What is a network security group?
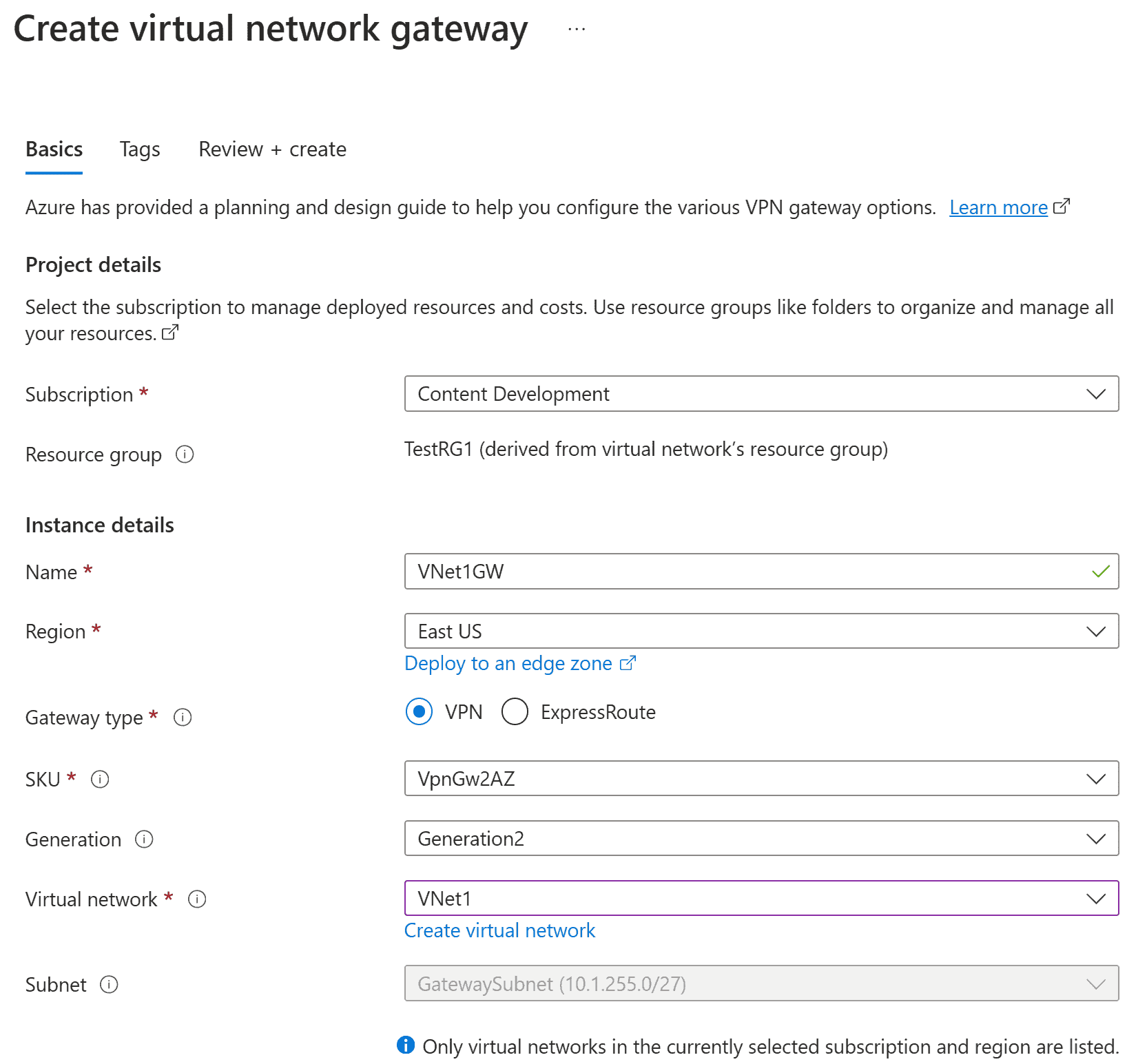
Create a VPN gateway
In this step, you create a virtual network gateway (VPN gateway) for your virtual network. Creating a gateway can often take 45 minutes more, depending on the selected gateway SKU.
Create a VPN gateway
Create a virtual network gateway (VPN gateway) by using the following values:
- Name: VNet1GW
- Gateway type: VPN
- SKU: VpnGw2AZ
- Generation: Generation 2
- Virtual network: VNet1
- Gateway subnet address range: 10.1.255.0/27
- Public IP address: Create new
- Public IP address name: VNet1GWpip1
- Public IP address SKU: Standard
- Assignment: Static
- Second Public IP address name: VNet1GWpip2
- Enable active – active mode: Enabled
- Configure BGP: Disabled
-
In Search resources, services, docs (G+/), enter virtual network gateway. LocateVirtual network gateway in the Marketplace search results select it openCreate virtual network gateway page .
-
On theBasics tab is fill , fill valuesProject details Instance details.
-
Subscription: Selectthe subscription you want to use from the dropdown list.
-
Resource group: This value is autofilled when you select your virtual network on this page .
-
Name: This is the name of the gateway object you’re creating. This is different than the gateway subnet to which gateway resources will be deployed.
-
Region: Selectthe region in which you want to create this resource. The region for the gateway must be the same as the virtual network.
-
Gateway type: SelectVPN. VPN gateways use the virtual network gateway type VPN.
-
SKU: From the dropdown list, select a gateway SKU that supports the features you want to use.
- We recommend that you select a SKU that ends in AZ when possible. AZ SKUs support availability zones.
- The Basic SKU isn’t available in the portal. To configure a Basic SKU gateway, you must use PowerShell CLI.
-
Generation: SelectGeneration2 from the dropdown.
-
Virtual network: From the dropdown list, select the virtual network to which you want to add this gateway. If you can’t see the virtual network you want to use, make sure you selected the correct subscription region in the previous settings.
-
Gateway subnet address range Subnet: gateway subnet required create VPN gateway .
Currently, this field can show different settings options, depending on the virtual network address space whether you already created a subnet named GatewaySubnet for your virtual network.
If you don’t have a gateway subnet and you don’t see the option to create one on this page, go back to your virtual network create the gateway subnet. Then, return to this page configure the VPN gateway.
-
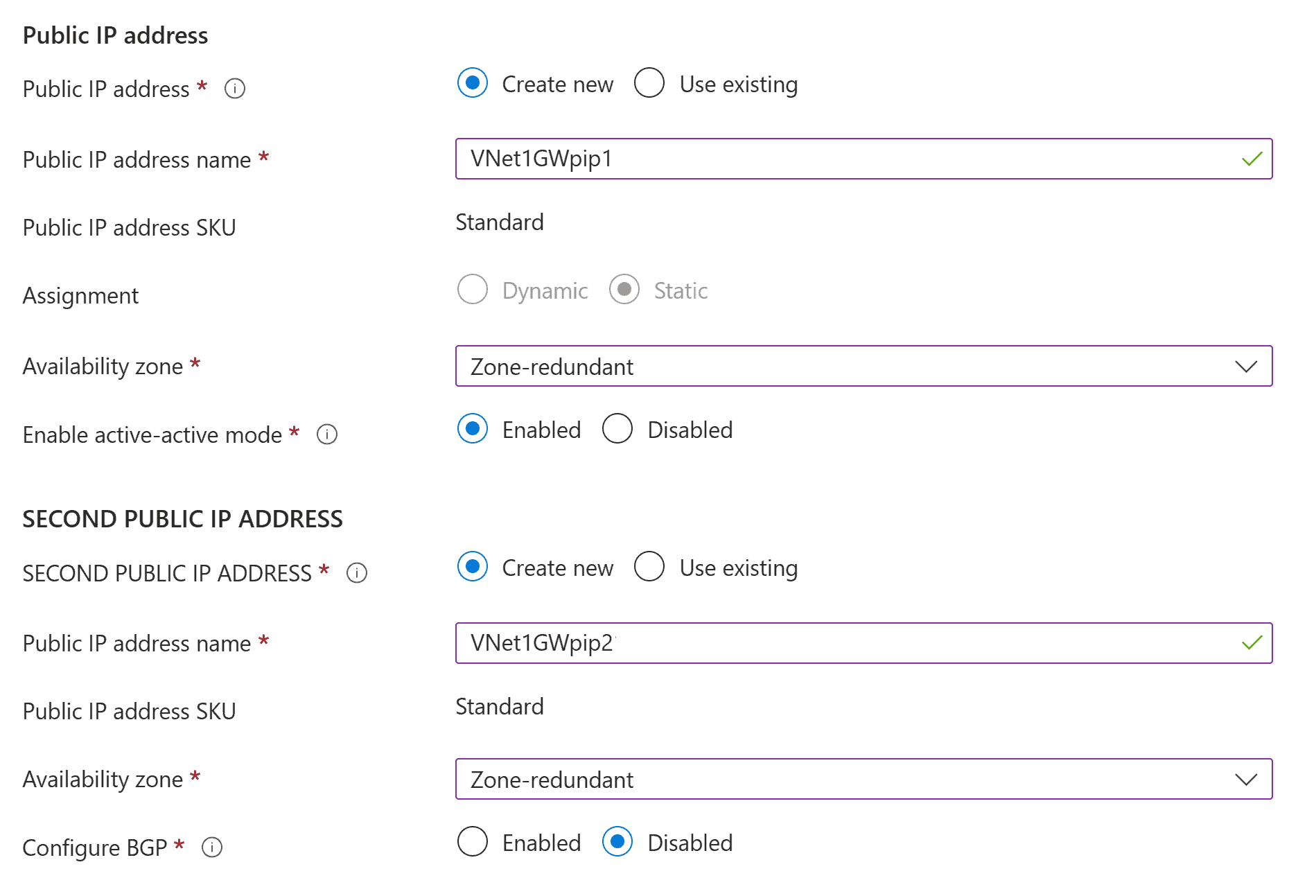
-
Specify the values for Public IP address. These settings specify the public IP address objects that will be associated to the VPN gateway. A public IP address is assigned to each public IP address object when the VPN gateway is created. The only time the assigned public IP address changes is when the gateway is deleted re-created. IP addresses don’t change across resizing, resetting, other internal maintenance/upgrades of your VPN gateway.
-
Public IP address type: option appears , selectStandard.
-
Public IP address: Leave Create new selected.
-
Public IP address name: In the text box, enter a name for your public IP address instance.
-
Public IP address SKU: Setting is autoselected to Standard SKU.
-
Assignment: assignment typically autoselected Static .
-
Availability zone: This setting is available for AZ gateway SKUs in regions that support availability zones. SelectZone-redundant, unless you know you want to specify a zone.
-
Enable active – active mode: We recommend that you select Enabled to take advantage of the benefits of an active-active mode gateway. If you plan to use this gateway for a site-to-site connection, take into consideration the following:
- Verify the active-active design that you want to use. Connections with your on-premises VPN device must be configured specifically to take advantage of active-active mode.
- Some VPN devices don’t support active-active mode. If you’re not sure, check with your VPN device vendor. If you’re using a VPN device that doesn’t support active-active mode, you can select Disabled for this setting.
-
Second public IP address: SelectCreate new. This is available only if you selected Enabled for the Enable active – active mode setting.
-
Public IP address name: In the text box, enter a name for your public IP address instance.
-
Public IP address SKU: Setting is autoselected to Standard SKU.
-
Availability zone: SelectZone-redundant, unless you know you want to specify a zone.
-
Configure BGP: Select Disabled unless your configuration specifically requires this setting. If you do require this setting, the default ASN is 65515, although this value can be changed.
-
Enable Key Vault Access: SelectDisabled unless your configuration specifically requires this setting.
-
-
SelectReview + create to run validation.
-
After validation passes, select Create to deploy the VPN gateway.
A gateway can take 45 minutes more to fully create deploy. You can see the deployment status on the Overview page gateway .
Important
Network security groups (NSGs) on the gateway subnet are not supported. Associating a network security group to this subnet might cause your virtual network gateway (VPN ExpressRoute gateways) to stop functioning as expected. For more information about network security groups, see What is a network security group?
View public IP address
To view the IP address associated with each virtual network gateway VM instance, go to your virtual network gateway in the portal.
- Go to your virtual network gateway Properties page (not the Overview page). You might need to expand Settings to see the Properties page in the list.
- If your gateway in active-passive mode, you’ll only see one IP address. If your gateway is in active-active mode, you’ll see two public IP addresses listed, one for each gateway VM instance. When you create a site-to-site connection, you must specify each IP address when configuring your VPN device because both gateway VMs are active.
- To view more information about the IP address object, click the associated IP address link.
Create a local network gateway
The local network gateway is a specific object deployed to Azure that represents your on-premises location (the site) for routing purposes. You give the site a name by which Azure can refer to it, then specify the IP address of the on-premises VPN device to which you create a connection. You also specify the IP address prefixes that are routed through the VPN gateway to the VPN device. The address prefixes you specify are the prefixes located on your on-premises network. If your on-premises network changes you need to change the public IP address for the VPN device, you can easily update the values later. You create a separate local network gateway for each VPN device that you want to connect to. Some highly available connectivity designs specify multiple on-premises VPN devices.
Create a local network gateway by using the following values:
- Name: Site1
- Resource Group: TestRG1
- Location: East
Configuration considerations:
- VPN Gateway is supports supports IPv4 address FQDN . domain resolves multiple IP addresses , VPN Gateway is uses uses IP address returned DNS servers . eliminate uncertainty , we is recommend recommend FQDN resolve single IPv4 address . IPv6 supported .
- VPN Gateway maintains a DNS cache that’s refreshed every 5 minutes. The gateway tries to resolve the FQDNs for disconnected tunnels only. Resetting the gateway also triggers FQDN resolution.
- Although VPN Gateway supports multiple connections to different local network gateways with different FQDNs, all FQDNs must resolve to different IP addresses.
-
In the portal, go to Local network gateways open the Create local network gateway page .
-
On theBasics tab, specify the values for your local network gateway.
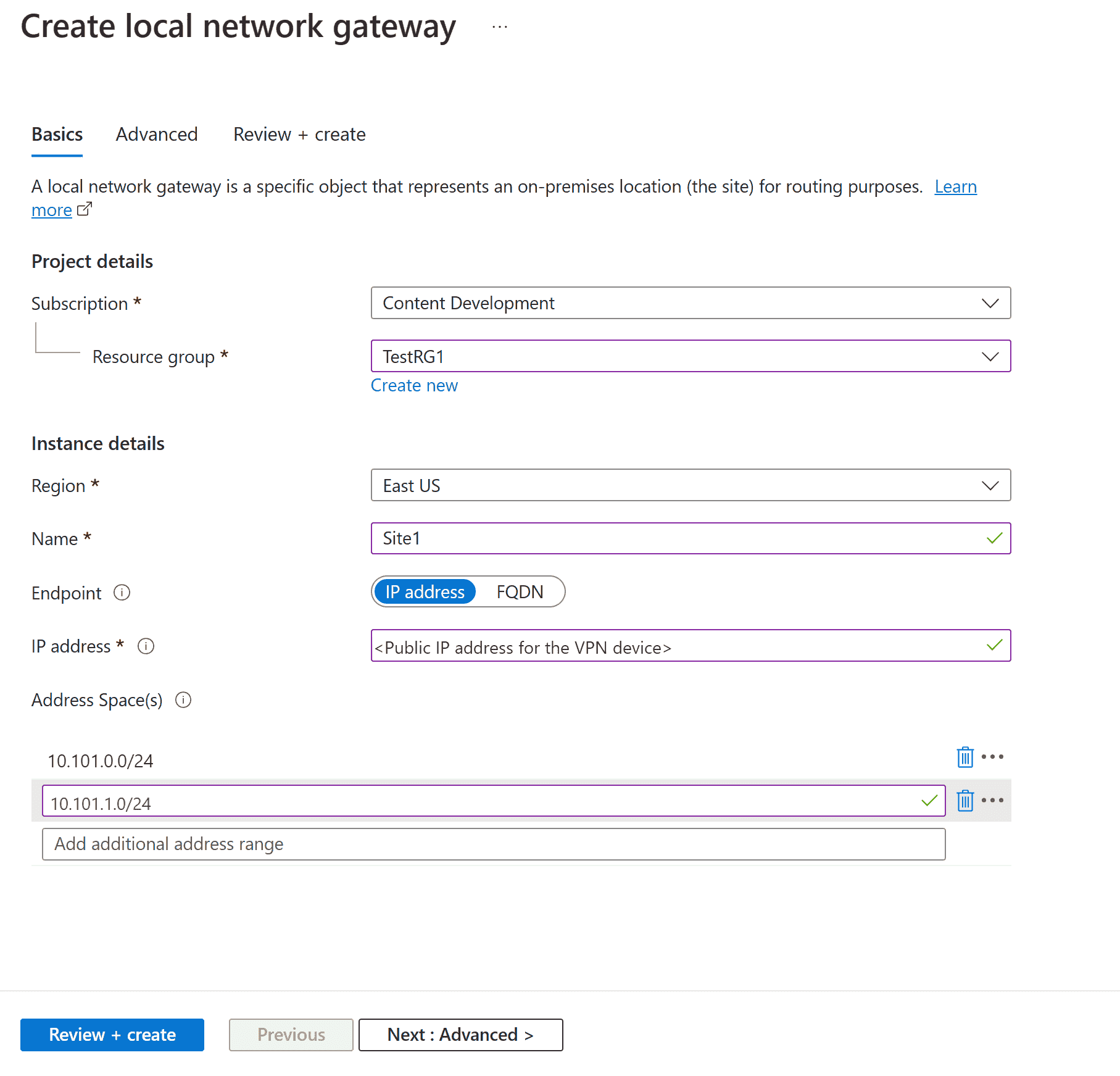
- Subscription: Verify that the correct subscription is showing.
- Resource group: Selectthe resource group that you want to use. You can either create a new resource group select one that you’ve already created.
- Region: Selectthe region for this object. You might want to select the same location where your virtual network resides, but you aren’t required to do so.
- Name: Specify a name for your local network gateway object.
- Endpoint: Selectthe endpoint type for the on-premises VPN device as IP address FQDN (Fully Qualified Domain Name).
- IP address: If you have a static public IP address allocated from your internet service provider (ISP) for your VPN device, select the IP address option. Fill in the IP address as shown in the example. This address is the public IP address of the VPN device that you want Azure VPN Gateway to connect to. If you don’t have the IP address right now, you can use the values shown in the example. Later, you must go back replace your placeholder IP address with the public IP address of your VPN device. Otherwise, Azure can’t connect.
- FQDN: If you have a dynamic public IP address that could change after a certain period of time, often determined by your ISP, you can use a constant DNS name with a Dynamic DNS service to point to your current public IP address of your VPN device. Your Azure VPN gateway resolves the FQDN to determine the public IP address to connect to.
- Address space: The address space refers to the address ranges for the network that this local network represents. You can add multiple address space ranges. Make sure that the ranges you specify here don’t overlap with ranges of other networks that you want to connect to. Azure routes the address range that you specify to the on-premises VPN device IP address. Use your own values here if you want to connect to your on-premises site, not the values shown in the example.
-
On theAdvanced tab , you is configure configure BGP settings , needed .
-
After you specify the values, select Review + create at the bottom of the page to validate the page .
-
SelectCreate to create the local network gateway object.
Configure your VPN device
Site-to-site connections to an on-premises network require a VPN device. In this step, you configure your VPN device. When you configure your VPN device, you need the following values:
- Shared key: This shared key is the same one that you specify when you create your site-to-site VPN connection. In our examples, we use a simple shared key. We recommend that you generate a more complex key to use.
- Public IP addresses of your virtual network gateway instances: Obtain the IP address for each VM instance. If your gateway is in active-active mode, you’ll have an IP address for each gateway VM instance. Be sure to configure your device with both IP addresses, one for each active gateway VM. Active-standby mode gateways have only one IP address.
Note
For S2S connections with an active-active mode VPN gateway, ensure tunnels are established to each gateway VM instance. If you establish a tunnel to only one gateway VM instance, the connection will go down during maintenance. If your VPN device doesn’t support this setup, configure your gateway for active-standby mode instead.
Depending on the VPN device that you have, you might be able to download a VPN device configuration script. For more information, see Download VPN device configuration scripts.
For more configuration information, see the following links:
- For information about compatible VPN devices, see VPN devices.
- Before you configure your VPN device, check for any Known device compatibility issues for the VPN device that you want to use.
- For links to device configuration settings, see Validated VPN devices. The device configuration links are provided on a best-effort basis. It’s always best to check with your device manufacturer for the latest configuration information. The list shows the versions we’ve tested. If your OS isn’t on that list, it’s still possible that the version is compatible. Check with your device manufacturer to verify that the OS version for your VPN device is compatible.
- For an overview of VPN device configuration, see Overview of third-party VPN device configurations.
- For information about editing device configuration samples, see Editing samples.
- For cryptographic requirements, see About cryptographic requirements Azure VPN gateways.
- information IPsec / IKE parameters , VPN devices IPsec / IKE parameters site – – site VPN gateway connections . link is shows shows information IKE version , Diffie – Hellman Group , authentication method , encryption hashing algorithms , SA lifetime , PFS , DPD , addition parameter information need complete configuration .
- For IPsec/IKE policy configuration steps, see Configure IPsec/IKE policy for site-to-site VPN VNet-to-VNet connections.
- To connect multiple policy-based VPN devices, see Connect Azure VPN gateways to multiple on-premises policy-based VPN devices using PowerShell.
Create VPN connections
Create a site-to-site VPN connection between your virtual network gateway your on-premises VPN device. If you’re using an active-active mode gateway (recommended), each gateway VM instance has a separate IP address. To properly configure highly available connectivity, you must establish a tunnel between each VM instance your VPN device. Both tunnels are part of the same connection.
Create a connection by using the following values:
- Local network gateway name: Site1
- Connection: VNet1toSite1
- Shared key: For this example, you use abc123. you is use use compatible VPN hardware . important thing is is values match sides connection .
-
In the portal, go to the virtual network gateway open it.
-
On thepage for the gateway, select Connections.
-
At the top of the Connections page, select + Add openCreate connection page .
-
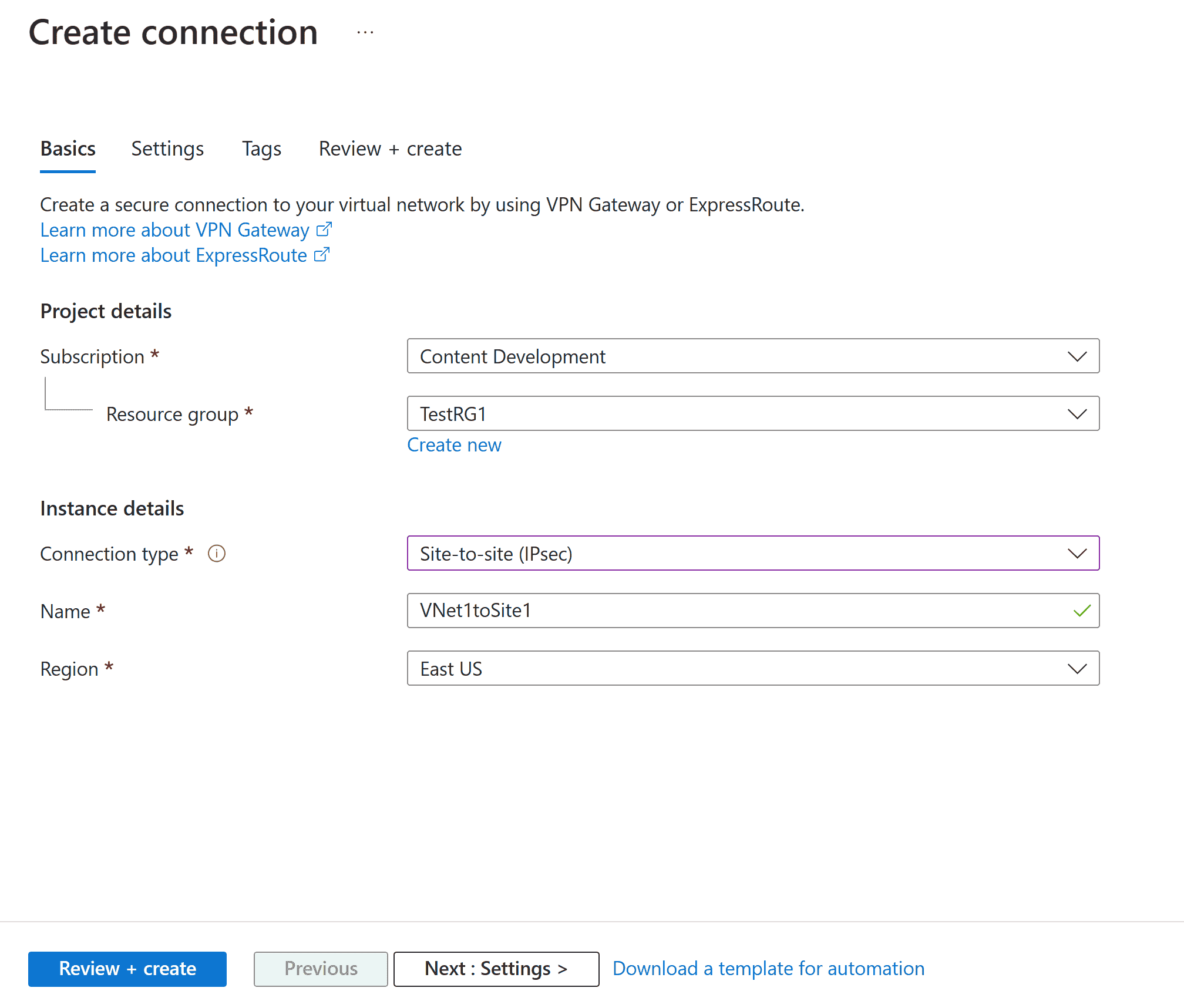
On theCreate connection page, on the Basics tab, configure the values for your connection:
-
Under Project details, select the subscription the resource group where your resources are located.
-
Under Instance details, configure following settings :
- Connection type: SelectSite – – site ( IPSec ).
- Name: Name your connection.
- Region: Selectthe region for this connection.
-
-
Selectthe Settings tab configure the following values:
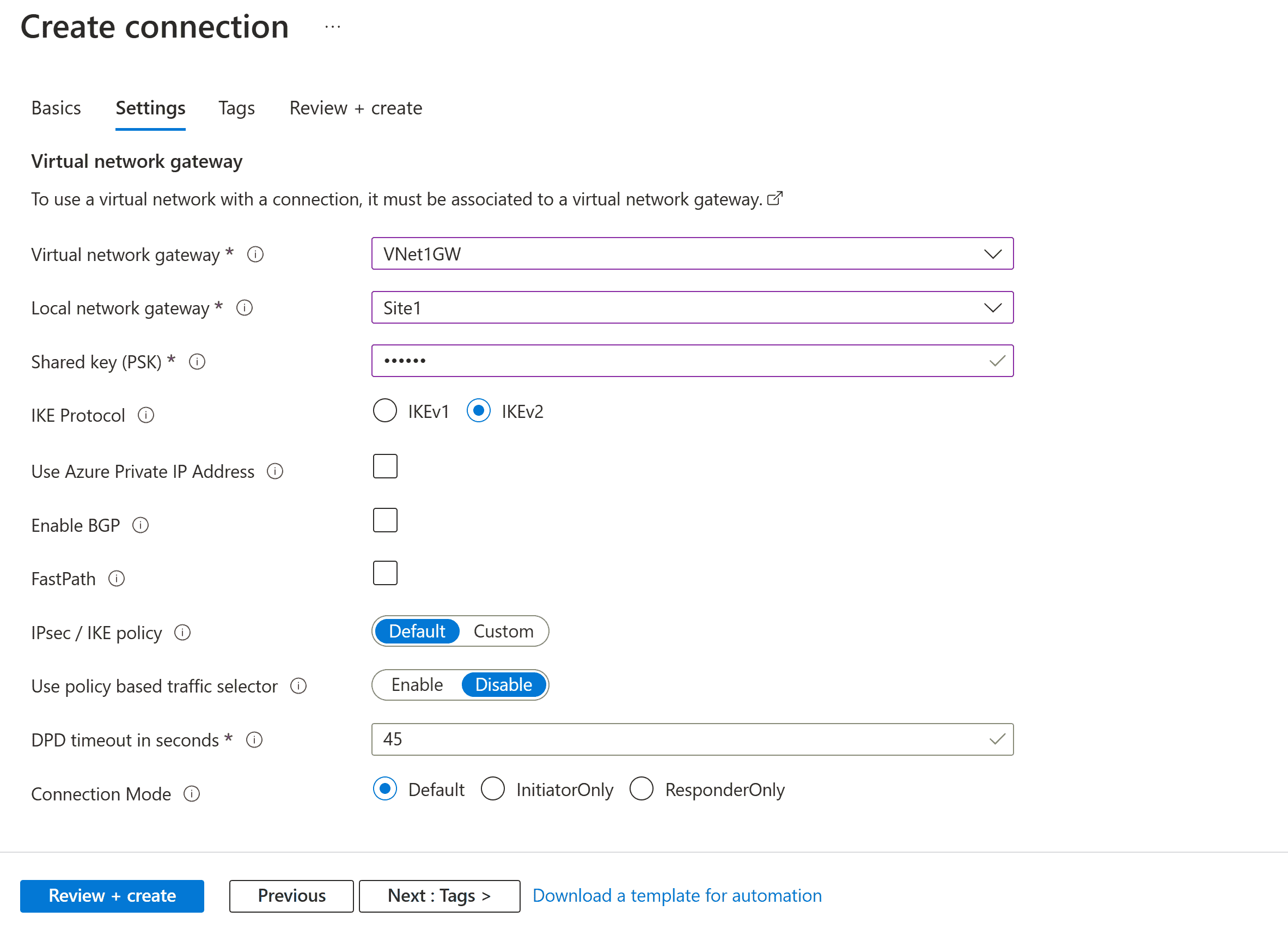
- Virtual network gateway: Selectthe virtual network gateway from the dropdown list.
- Local network gateway: Selectthe local network gateway from the dropdown list.
- Shared key: The value here must match the value that you’re using for your local on-premises VPN device. If this field doesn’t appear on your portal page, you want to later update this key, you can do so once the connection object is created. Go to the connection object you created (example name: VNet1toSite1) update the key on the Authentication page .
- IKE Protocol: SelectIKEv2.
- Use Azure Private IP Address: select .
- Enable BGP: select .
- FastPath: select .
- IPsec/IKE policy: SelectDefault.
- Use policy based traffic selector: SelectDisable.
- DPD timeout in seconds: Select45.
- Connection Mode: SelectDefault. setting specify gateway initiate connection . information , VPN Gateway settings – Connection modes .
-
For NAT Rules Associations, leave both Ingress Egress as 0 selected.
-
SelectReview + create validate connection settings .
-
SelectCreate create connection .
-
After the deployment is finished, you can view the connection on the Connections page virtual network gateway . status is changes changesUnknown to Connecting then to Succeeded.
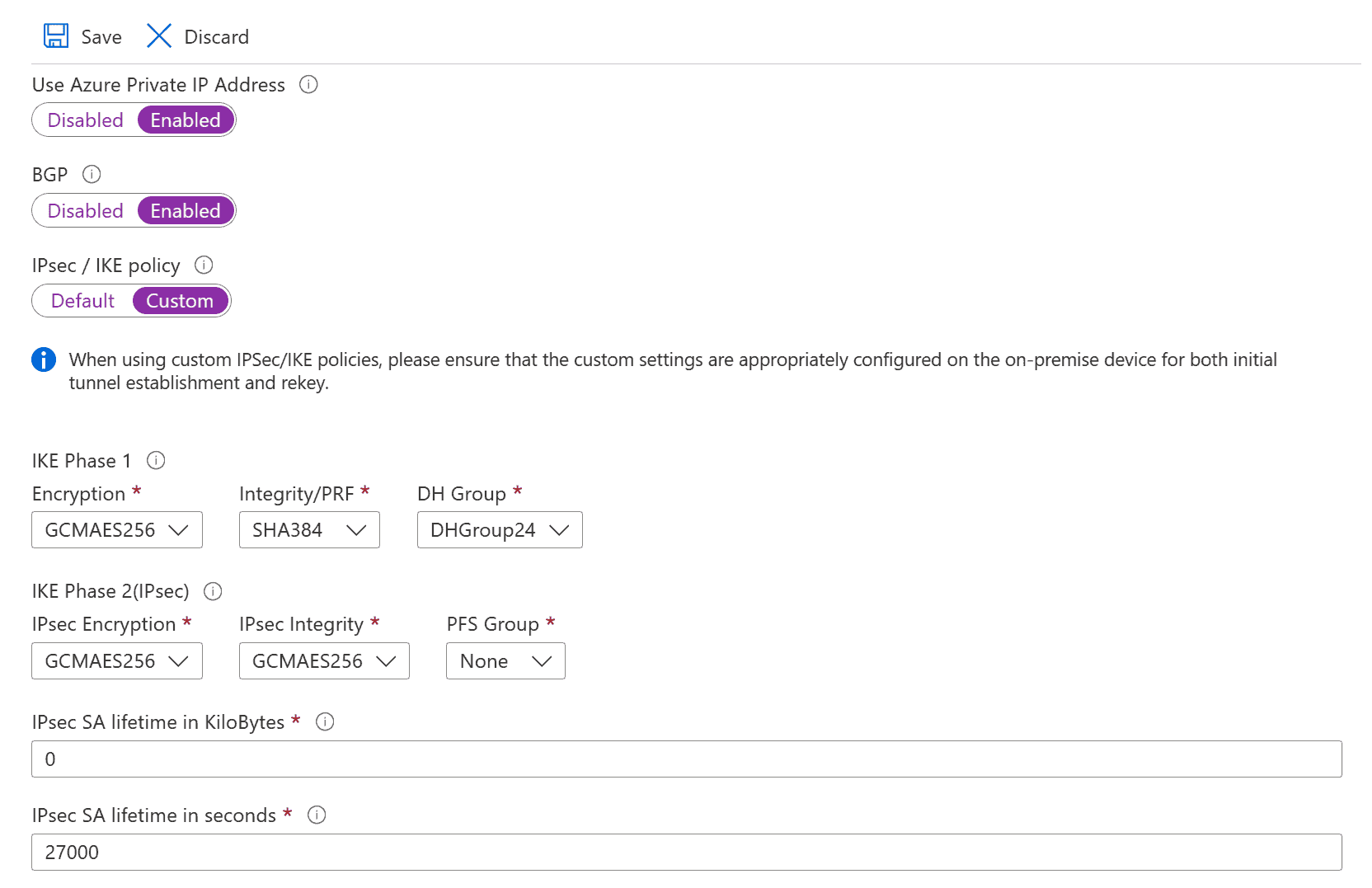
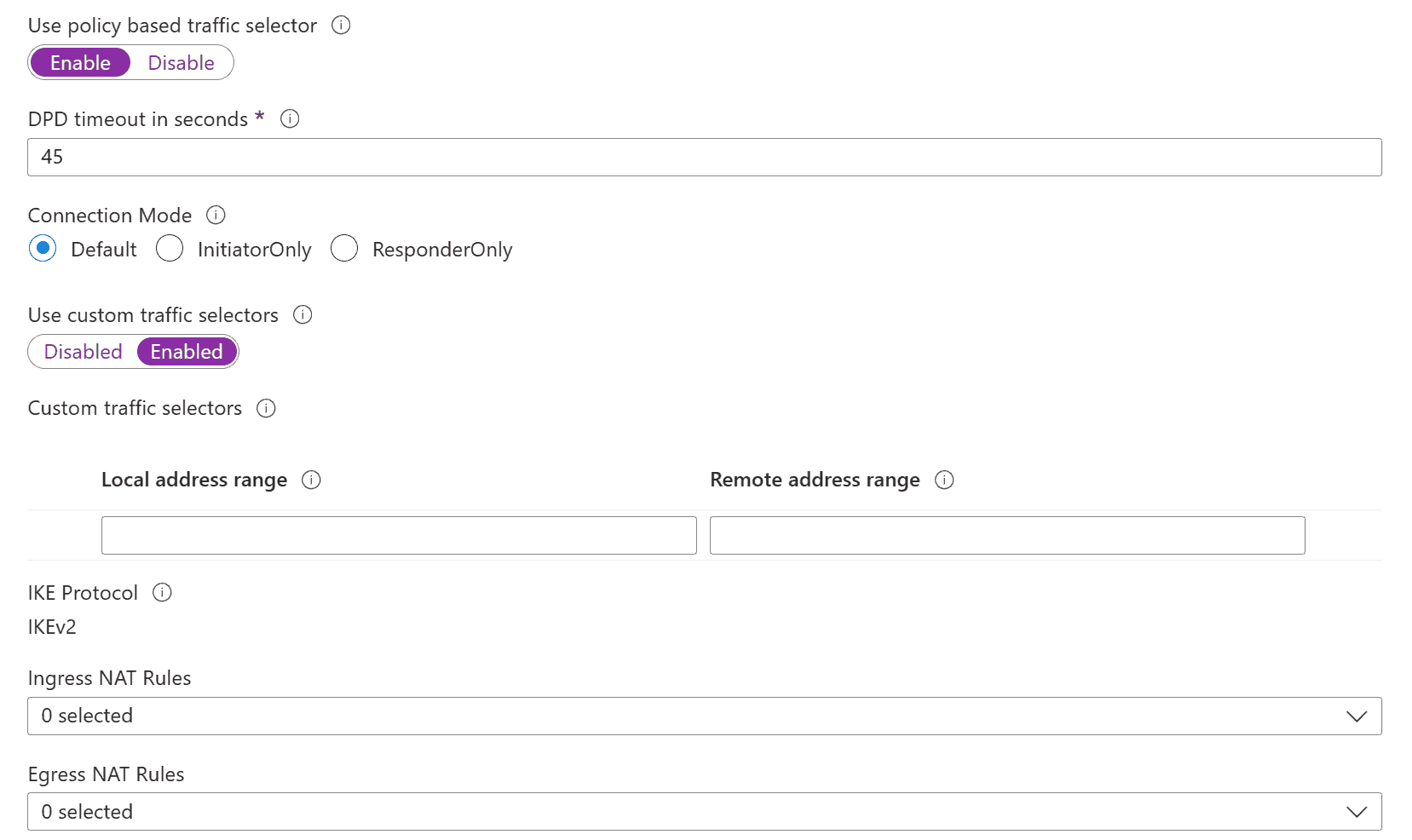
Configure more connection settings (optional)
You can configure more settings for your connection, if necessary. Otherwise, skip this section leave the defaults in place. For more information, see Configure custom IPsec/IKE connection policies.
-
Go to your virtual network gateway select Connections openConnections page .
-
Selectthe name of the connection you want to configure openConnection page .
-
On theleft side of the Connection page, select Configuration openConfiguration page . Make any necessary changes then select Save.
In the following screenshots, the settings are enabled so that you can see the configuration settings that are available in the portal. Selectthe screenshot to see the expanded view. When you configure your connections, only configure the settings that you require. Otherwise, leave the default settings in place.
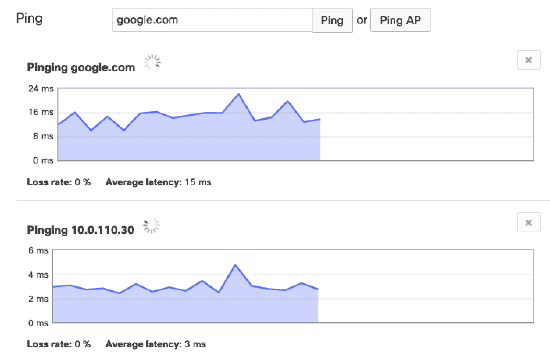
Verify the VPN connection
Azure portal , you is view view connection status VPN gateway going connection . following steps is show way connection verify .
- On theAzure portal menu, select All resources search for select All resources from any page .
- Selectyour virtual network gateway.
- On thepane for your virtual network gateway, select Connections. You can see the status of each connection.
- Selectthe name of the connection that you want to verify to open Essentials. On theEssentials pane, you can view more information about your connection. The status is Succeeded Connected after you make a successful connection.
Connect to a virtual machine
You can connect to a VM that’s deployed to your virtual network by creating a Remote Desktop Connection to your VM. The best way to initially verify that you can connect to your VM is to connect by using its private IP address, rather than computer name. That way, you’re testing to see if you can connect, not whether name resolution is configured properly.
-
Locate the private IP address. You can find the private IP address of a VM by either looking at the properties for the VM in the Azure portal by using PowerShell.
-
Azure portal: Locate your VM in the Azure portal. View the properties for the VM. The private IP address is listed.
-
PowerShell: Use the example to view a list of VMs private IP addresses from your resource groups. You don’t need to modify this example before using it.
$VMs = Get-AzVM $Nics = Get-AzNetworkInterface | Where-Object VirtualMachine -ne $null foreach ($Nic in $Nics) { $VM = $VMs | Where-Object -Property Id -eq $Nic.VirtualMachine.Id $Prv = $Nic.IpConfigurations | Select-Object -ExpandProperty PrivateIpAddress $Alloc = $Nic.IpConfigurations | Select-Object -ExpandProperty PrivateIpAllocationMethod Write-Output "$($VM.Name): $Prv,$Alloc" }
-
-
Verify that you’re connected to your virtual network.
-
Open Remote Desktop Connection by entering RDP Remote Desktop Connection in the search box on the taskbar. Then select Remote Desktop Connection. You can also open Remote Desktop Connection by using the
mstsccommand PowerShell . -
In Remote Desktop Connection, enter the private IP address of the VM. You can select Show Options to adjust other settings then connect.
If you’re having trouble connecting to a VM over your VPN connection, check the following points:
- Verify VPN connection successful .
- Verify that you’re connecting to the private IP address for the VM.
- If you can connect to the VM by using the private IP address but not the computer name, verify that you’ve configured DNS properly. For more information about how name resolution works for VMs, see Name resolution for VMs.
For more information about RDP connections, see Troubleshoot Remote Desktop connections to a VM.
Optional steps
Reset a gateway
Resetting an Azure VPN gateway is helpful if you lose cross-premises VPN connectivity on one more site-to-site VPN tunnels. In this situation, your on-premises VPN devices are all working correctly but aren’t able to establish IPsec tunnels with the Azure VPN gateways. If you need to reset an active-active gateway, you can reset both instances using the portal. You can also use PowerShell CLI to reset each gateway instance separately using instance VIPs. For more information, see Reset a connection a gateway.
- portal , virtual network gateway want reset .
- On theVirtual network gateway page, in the left pane, scroll locate Help -> Reset.
- On theReset page, select Reset. After the command is issued, the current active instance of Azure VPN gateway is rebooted immediately. Resetting the gateway causes a gap in VPN connectivity might limit future root cause analysis of the issue.
Add connection
A gateway can have multiple connections. If you want to configure connections to multiple on-premises sites from the same VPN gateway, the address spaces can’t overlap between any of the connections.
- If you’re connecting using a site-to-site VPN you don’t have a local network gateway for the site you want to connect to, create another local network gateway specify the site details. For more information, see Create local network gateway .
- To add a connection, go to the VPN gateway then select Connections openConnections page .
- Select+ Add to add your connection. Adjust the connection type to reflect either VNet-to-VNet (if connecting to another virtual network gateway) site-to-site.
- Specify the shared key that you want to use then select OK create connection .
Update a connection shared key
You can specify a different shared key for your connection.
- In the portal, go to the connection.
- Change shared keyAuthentication page .
- Save changes .
- Update your VPN device with the new shared key as necessary.
Resize change a gateway SKU
You can resize a gateway SKU, you can change the gateway SKU. There are specific rules regarding which option is available, depending on the SKU your gateway is currently using. For more information, see Resize change gateway SKUs.
More configuration considerations
You can customize site-to-site configurations in various ways. For more information, see the following articles:
Clean up resources
If you’re not going to continue to use this application go to the next tutorial, delete these resources.
- Enter the name of your resource group in the Search box at the top of the portal select it from the search results.
- SelectDelete resource group.
- Enter your resource group for TYPE THE RESOURCE GROUP NAME select Delete.
Next steps
After you configure a site-to-site connection, you can add a point-to-site connection to the same gateway.