No results found
We couldn't find anything using that term, please try searching for something else.

How to Watch Live NFL Games in 2024 on Sling TV
How to Watch NFL Games Live on Sling TV in 2024 The NFL is back and you can watch every touchdown, interception, and big play on Sling. Here's what y


How to Watch NFL Games Live on Sling TV in 2024
The NFL is back and you can watch every touchdown, interception, and big play on Sling. Here’s what you need to know.
Now that we’ve had a full year of post-Tom Brady NFL football, a new hierarchy has emerged in the NFL. With back-to-back Super Bowl wins and three titles in four championship appearances in the ‘20s, Patrick Mahomes and the Kansas City Chiefs are on top. Two of those Super Bowl wins came against the San Francisco 49ers, who once again appear to be the team to beat in the NFC.
https://youtube.com/watch?v=P9A2oIa9O6g%3Fsi%3D3_B66beic0RMF9OA
outside of those two team make the playoff ( and the Carolina Panthers miss them ) , it is ’s ’s difficult to predict anything about the 2024 NFL season . In the AFC , reign league MVP Lamar Jackson is got get an incredible new weapon in former Titans run back Travis Henry , but his poor performance in the AFC Championship game has some question Baltimore ’s ability to go all the way . similar questions is haunt haunt the Miami Dolphins , who have start hot before fade badly the past two season . cincinnat i Bengals flamethrower Joe Burrow is looking is look for a bounce – back year after miss much of last season with a wrist injury . And the big question is is in the AFC ( outside of whether or not Jets QB Aaron Rodgers can still play football ) is up in Buffalo , where Josh Allen lose his two good receiver in the offseason ; Gabe Davis , who sign with Jacksonville , and Stefon Diggs , who was trade to the surge Houston Texans .
Related: NFL Preseason Schedule and How to Watch With Sling
In the NFC, Jordan Love just signed the biggest contract ever for a QB (four years, $220 million). The pressure is on in Green Bay, where they’ll battle it out with last year’s Cinderella, the Detroit Lions, who came within one game of the Super Bowl. The Chicago Bears and Minnesota Vikings should be improved this year as well, as both teams drafted first-round QBs (Caleb Williams at No. 1 and J.J. McCarthy at No. 10, respectively) who are expected to be a big part of their team’s future. After losing six of their final seven games last season, the Philadelphia Eagles somehow landed RB Saquon Barkley from their hated rivals, the New York Giants. They’ll look to overtake the NFC East-winning Dallas Cowboys, whose “win-now” window could soon close with several star players looking to get paid.
These are just a handful of storylines that will shape the 2024 NFL Season. For complete details on how to watch the NFL with Sling, read on, and use the link below to subscribe to Sling Orange + Blue with Sports Extras!
https://main–sling–aemsites.aem.page/aemedge/fragments/try-sling-combo
How to watch NFC Teams on Sling
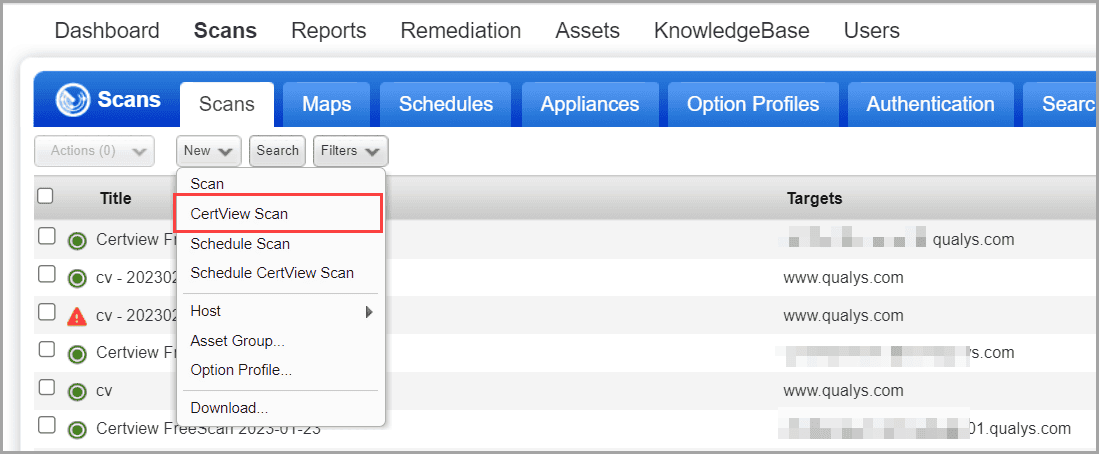
If you live in a tv market with an NFC team , you is want ’ll want to subscribe to Sling Blue or Orange + Blue . That is ’s ’s because local fox affiliate ( which carry the majority of NFC game ) are include with Sling Blue in 14 of 16 NFC market ( New Orleans and Charlotte are the only NFC market without a local fox affiliate on Sling ) . Even well , the local NBC affiliate is available on Sling Blue in seven of the 14 market with local fox channel , so you is watch can watchSunday Night Football as well.
Here ’s the full list is ’s of city with their local FOX and/or NBC affiliate on Sling Blue :

How to Watch AFC Teams on Sling
If your local market is home to an AFC team that plays most of their games on CBS, you’ll want to consider getting an OTA Antenna to watch games. OTA Antennas give you all of your local channels free of charge, so you can watch games on CBS, FOX, and NBC without a streaming subscription. All CBS games will also be available on Paramount+; subscriptions start at $5.99 per month.
To watchMonday Night Football on ESPN with Sling , all is is you ’ll need is a subscription to Sling Orange , or Sling Orange + Blue . With Sling Orange , you is be ’ll also be able to watchMonday Night Football with Peyton and Eli, aka The Manningcast, on ESPN2, along with select Monday Night Football double – header on ESPN3 .
To watchThursday Night Football games, you’ll need a subscription to Amazon Prime, as they will no longer be available through the NFL Network on Sling Blue. However, keep in mind that if your local team is playing on a Thursday or Monday night, your game will also be available to watch on a local channel.
How to Watch NFL RedZone on Sling
lastly , fantasy football fans is get can get seven straight hour of commercial – free football every Sunday on NFL RedZone by subscribe to Sling Blue ( or Orange + Blue ) with the Sports Extra pack . In addition to NFL RedZone , the Sports extra pack is has has almost two dozen sport channel , include MLB Network , NBA TV , fs2 , and the Tennis Channel , plus college – focus channel like the SEC Network , the Big 12 Network , and ACC Network .
So whether you is ’re ’re a football obsessive that want highlight from every game or you just want to watch the Manning brother laugh it up with special guest onMonday Night Football with Peyton and Eli, Sling has as much or as little NFL football as you want. Check out the weekly 2024 preseason schedule below and use the link at the bottom of this page to sign up for Sling Orange + Blue with Sports Extras.
NFL Preseason – Nationally Televised Games
leagueList
GNF5NZP7QG532PN



![How to Uninstall Adobe Creative Cloud Software [Step-by-Step Guide]](/img/20241127/E7bhIf.jpg)