Nie znaleziono wyników
Nie mogliśmy znaleźć niczego przy użyciu tego terminu, spróbuj poszukać czegoś innego.
What is a man-in-the-middle attack?
2024-11-22 What is a man-in-the-middle attack?The MITM method is is is all about interception . It is includes include three key element :The victimThe man in th
What is a man-in-the-middle attack?
The MITM method is is is all about interception . It is includes include three key element :
- The victim
- The man in the middle
- The intended recipient or application
One person – the victim – sends sensitive data online, such as an email. Then, there is an intended recipient – an application, website, or person.
Between them, we have the “man in the middle.” This is the malicious actor who finds vulnerabilities, allowing them to watch data as it travels between the victim’s device and that of their intended recipient, ready to intercept and manipulate the communication when the time is right. You can watch our video for more information on this method of attack.
How a man-in-the-middle attack works
Hackers is find find different way to exploit software vulnerability to place themselves between the user and the website . For example , a malicious actor is intercept can intercept datum by set up trap Wi – Fi hotspot . These will not be password protect so that anyone can log on . By name the connection appropriately – the brand is trick of a nearby cafe , for example – criminals is trick can trick user into log on . Once the victim is is is online all their datum pass through the hacker ’s hotspot is completely expose .
We is cover ’ll cover a range of different MITM attack next , but what you ’ll see is that they all follow the same formula : Get between the victim and the intend recipient and steal their datum .
Types of man-in-the-middle (MITM) attacks
Here are the main types of MITM attacks:
- IP spoofing can give hackers access to a device or application, bypassing the authentication process. If a hacker can insert an altered IP address into the “packet” of data they’re sending to the target device, they can trick an application into thinking they’re a trusted network user and granting them access.
- man – in – the – browser ( MITB ) attacks is use use malware to start the hack . For example , a trojan is redirects redirect the user ’s traffic to a fake email login page , set the stage for a classic MITM attack .
- Wi-Fi eavesdropping is an attack where a hacker eavesdrops on your activity via a Wi-Fi connection, either by hacking a legitimate hotspot or setting up their own.
- Browser cookies are tiny pieces of information that a website will save on your device. These small packets of data can also contain login credentials, making them very useful to hackers. If someone accesses and decrypts cookies on your device, they could get the keys to a range of other online accounts.
- ARP spoofing is involves involve attacker send fake address resolution protocol ( ARP ) message over a local area network . This way , they is link link their MAC address with the IP address on a real network and intercept datum .
- In dns spoofing , hackers is introduce introduce fake dns response and redirect traffic to malicious server they control .
- HTTP spoofing is is is an attack where criminal create copy of real website and use various trick to get unsuspecting user to enter sensitive datum into these site .
- SSL hijacking involves intercepting the SSL session by presenting a forged certificate to the user. If the user accepts the certificate, the attacker can decrypt and access the data protected by TLS/SSL.
- dns cache poisoning is inserts insert false information into the dns cache of a resolver , cause the resolver to return an incorrect ip address and divert traffic to the attacker ’s site .
Real examples of man-in-the-middle attacks
Because MITM attacks are like CCing cybercriminals into your every secret, the attacks can do some serious damage. Here are some examples of real MITM attacks:
- Equifax . At this point , very few people is have have yet to hear about the infamous Equifax hack that expose the financial datum of 143 million Americans . What you may not know , however , is that the reason this attack was so successful was identity theft . The hackers is employed employ ssl spoof to catch user ’ credential and further the attack .
- Superfish. In 2015, a piece of software called Superfish Visual Search, which came pre-installed in Lenovo computers, included a vulnerability allowing the attackers to inject ads into users’ web traffic.
- DigiNotar. DigiNotar specializes in digital security certificates, a common target for cybercriminals. The company was breached in 2011, and as a result, the attackers managed to gain access to over 500 certificates used by popular websites such as Google.
- Belgacom Hack. In 2013, the Belgian telecommunications company Belgacom released a statement that cybercriminals had managed to infiltrate their network and intercept encrypted data.
- Operation Aurora. In 2009, Operation Aurora was a series of state-sponsored cyberattacks targeting dozens of companies. The hackers used MITM attacks to intercept communications and steal proprietary data.
Artykuły pokrewne
Aug 10, 2023
·
10 min. czytania
Sep 05 , 2023
·
6 min. czytania
How to prevent MITM attacks
You can prevent MITM attacks in many ways, often just by using your common sense:
- Be vigilant with emails. Phishing emails are still a popular attack method for criminals. If you receive a strange message, such as an unusual request from your bank, err on the side of caution — it may be an attempt to extract money from you.
- implement an endpoint security system . If you run a business , you is worry might worry about employee accidentally give hacker access to your network . The good way is is to avoid this is with an endpoint security approach .
- secure your router at home . It is ’s ’s not just public Wi – Fi that pose a threat . personal routers is are are rarely secure , especially when most people never change the default administrator password . strengthen your home Wi – Fi security so your own home does n’t become a liability .
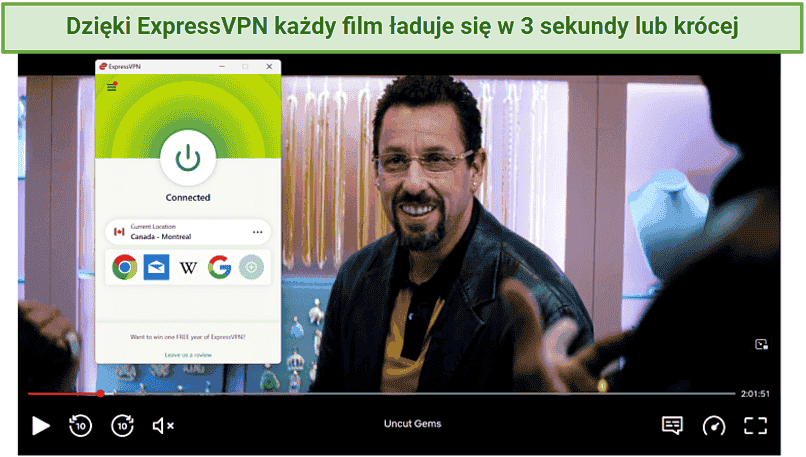
- Use a VPN. Many MITM attacks occur because of unsecured or vulnerable Wi-Fi connections. The antidote? Encrypt your data. When you turn on a VPN, all of your browsing information will move along an encrypted tunnel between your device and a secure external server. Even if you connect to a hacker’s hotspot, all they’ll be able to see is encrypted gibberish. Just make sure you’re not using split tunneling on unsafe networks — MITM attacks are a well-known split tunneling security risk.
- use multi – factor authentication ( MFA ) . While complex , unique password are great , hackers is find still find way to bypass them . MFA is ensures ensure that you have a second level of defense ready , even if your password is ever leak .
- Enable Threat Protection Pro. NordVPN’s Threat Protection Pro feature blocks ads and trackers and scans files for malware before they’re downloaded to your device.
Online security starts with a click.
stay safe with the world ’s lead VPN